For the full report please read the "EPQ Written Report.pdf" file.
Windows Encryption program developed as part of my EPQ qualification.
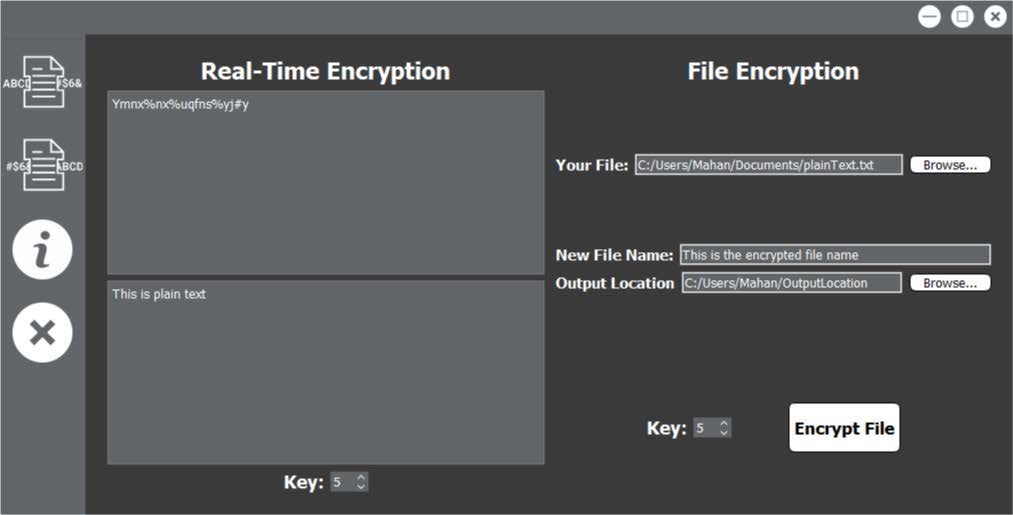
For my Extended Project Qualification (EPQ), I decided to explore security and encryption and build a program that can encrypt and decrypt text files. The first part of my research was spent researching which programming languages would benefit me the most and any frameworks that were useful to my program. The second part of my research was exploring encryption methods and which method I could use to implement into my program.
This program was developed using the QT framework built using C++.
This is the final version as of now
This program uses the Vigenère cipher algorithm which is an extended version of the Caesar Cipher algorithm. A string of letters of length 4-12 is used ask the key to shift the letters. By calculating how many possible combinations my keys could have and by estimating how many keys can be tested per second, we can calculate an estimate as to how secure the keys are. My keys used in my program are randomly generated between the lengths of 4 to 12 characters. Each character is chosen randomly from 90 possible values from the ASCII table. Therefore, each letter can have 90 combinations. This means that to crack a key of length 12 characters, 90^12 combinations need to be tested (near to 3x10^23 combinations). According to research from “BetterBuys.com”, the estimated number of keys testable in one second in 2018 is around 15 million keys per second. This means that it would take 2x1016 (3x10^23/15000000) seconds to test every single possible combination of my keys. This translates to 6x10^8 years to crack one of my keys. This is an astronomically large amount of time, so this means that realistically, this key is uncrackable through brute force.
To test this for myself, I used the estimating cracking time program available on “BetterBuys.com” to get an estimate of how long randomly generated keys from my program would take to be cracked. I took a sample of 100 keys randomly generated from my program, put into the websites estimator and recorded the given time in years it would take to crack that key. The graph below shows the result of this experiment. It shows the percentage of time a key was generated that had a certain average time to crack. This showed that more than 50% of the time a key is generated takes over 91,458 years to crack. These results show that in practice, these keys are just as reliable and secure as thought to be in theory.
At this point into the project I was happy with the design and I wanted to implement the final encryption algorithms and the final changes that were needed to be made. I decided to change the Caesar Cipher encryption algorithm from using a number key to using my implementation of word key. It is very similar to the previous version except for some back-end tweaks. I have implemented my implementation of the Caesar Cipher key in form of a word which can be randomly generated by clicking the “Random Key” button or if it is left blank when the user types in their message, the program will automatically generate a random key, only if the field is empty. For decryption, the user is not allowed to type in their cypher text until they have entered a key. An error message shows if the user tries to enter their cypher text before entering the key. They key itself is generated using randomising algorithms and gives back an ASCII value which can be corresponded to a character. This way the key is a word and not just a single number, therefore, the algorithm is more secure. I also implemented a method of hiding the key in the cypher text of the encrypted file. The placement of the key is known by the algorithm so it is easy for the program to find the key.